Our Mission: Uniting Technology and Business for Maximum Efficiency
At Unified Solutions, we pride ourselves on our unwavering commitment to innovation, integrity, and the highest standards of customer satisfaction. Our core mission is to provide businesses and individuals with cutting-edge technology that enables them to thrive in an ever-evolving digital landscape. We place a strong emphasis on collaboration, working closely with our clients to fully understand address their unique IT needs, demonstrating determination and expertise in every project we undertake. Our dedicated team is focused on delivering reliable, customized solutions that not only drive success, but also enhance operational efficiency and ensuring that our clients can confidently navigate complexities of the modern technological world.

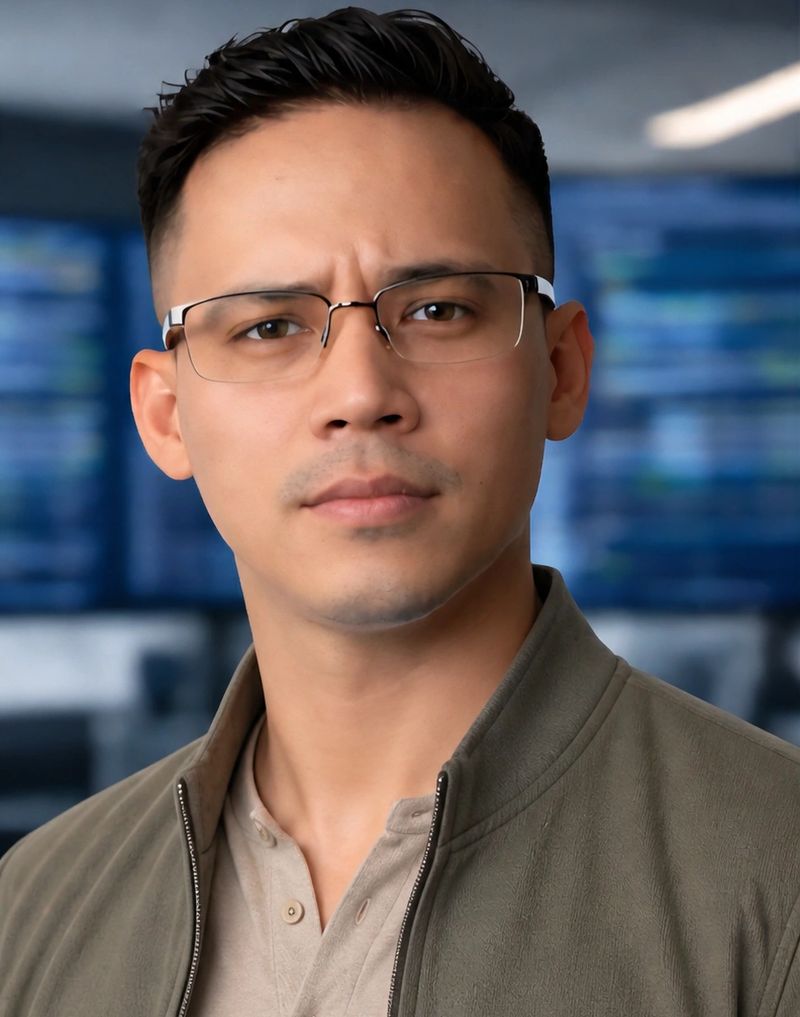
Our Program Specialist is the architect behind the scenes—the one turning ideas into working systems.
With a strong background in software development and automation, they design and build custom applications, optimize performance, and solve complex technical challenges. Whether it’s developing scalable platforms, integrating APIs, or fine-tuning logic for efficiency, they ensure every line of code serves a purpose.
What they bring:
- Custom software development & automation
- System architecture & API integrations
- Debugging, optimization, and performance tuning
- Turning real-world problems into elegant technical solutions

The backbone of daily operations, our IT Specialist keeps everything running smoothly and efficiently.
From setting up networks and managing servers to troubleshooting issues and supporting users, they ensure that systems stay online, fast, and reliable. They’re the go-to expert for infrastructure, making sure technology works exactly how it should—when it should.
What they bring:
- Network setup, maintenance, and optimization
- Server management & system administration
- Hardware/software support and troubleshooting
- Backup solutions, system migrations, and reliability planning
Our Surveillance Specialist ensures that every environment is seen, understood, and protected—24/7.
With deep expertise in modern camera systems and monitoring technologies, they design and implement surveillance solutions that provide clear visibility and real-time awareness. From strategic camera placement to advanced video analytics, they make sure nothing important goes unnoticed.
What they bring:
- CCTV and IP camera system design & installation
- Mobile access configuration
- Video management systems (VMS) and storage optimization
- Smart analytics (motion detection, alerts, AI-based recognition, custom detection zones)
- Troubleshooting, maintenance, and system upgrades
- Teach system configurations/ training on operating system
Our Integrated Business Solutions

Ubiquiti
provides a unified ecosystem of networking, Wi-Fi, and surveillance equipment designed to deliver enterprise-level performance with simple, centralized management. Through its Unifi platform, users can control routers, switches, access points, cameras, and access control systems from a single interface, making it highly scalable for both small businesses and large environments. Known for its reliability, cost-effectiveness, and lack of recurring licensing fees, Ubiquiti is a popular choice for building secure, high-performance, and easily managed IT infrastructure.
Full IT infrastructure installs
this involves the complete design, deployment, and configuration of all technology systems required to support an organization’s daily operations. This process begins with building a reliable network infrastructure, including routers, switches, firewalls, and secure wireless access points, all configured for performance, segmentation, and redundancy. It also includes setting up servers and computing environments, whether physical or virtual, to host critical services such as domain control, file storage, and business applications.
In addition, all endpoint devices such as desktops, laptops, and mobile devices are configured with standardized operating systems, required software, and secure user access. Identity and access management is implemented through systems like Active Directory or cloud-based solutions, ensuring proper role-based permissions, group policies, and multi-factor authentication for security. Cybersecurity measures are integrated throughout the infrastructure, including firewalls, endpoint protection, monitoring systems, and regular patch management to protect against threats.
Backup and disaster recovery solutions are also established to ensure business continuity, with automated backups, secure storage, and recovery planning in place. Where needed, cloud services are integrated to support collaboration, storage for deployment to support internal and external communication.
Finally, monitoring and management tools are implemented to provide real-time visibility into system performance and health, along with documentation and training to ensure long-term usability and support. The end result is a secure, scalable, and efficient IT environment designed to support current needs while allowing for future growth.
Continued business development and security monitoring
This involves the ongoing management, optimization, and protection of an organization’s IT environment to ensure long-term growth, efficiency, and resilience. This includes continuously evaluating and improving systems, processes, and technologies to align with evolving business needs, while proactively identifying opportunities for increased performance, scalability, and cost efficiency.
At the same time, comprehensive security monitoring is maintained to safeguard the organization against emerging threats